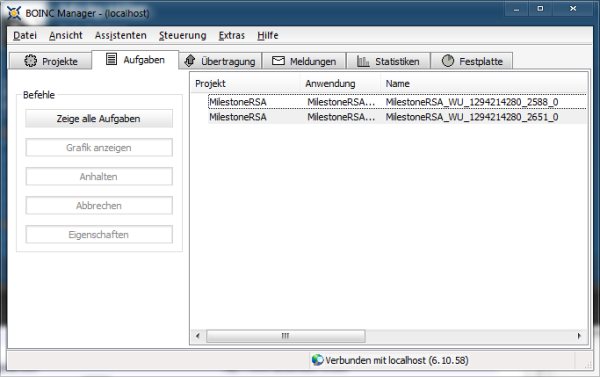
MilestoneRSA ist ein BOINC Projekt welches sich zur Aufgabe gemacht hat den Milestone 1024bit RSA Key per Brutforce zuknacken, würde das geklingten könnte man eigene Recovery Images signieren und damit Custom ROMs nutzen. Sicherlich ist es eher unwahrscheinlich den Key mit dieser Methode rauszubekommen, doch ich bin mit den andern 1411 Nutzer der Hoffnung irgendwann ein offenes Milestone zuhaben 😉
About MilestoneRSA
MilestoneRSA is a boinc project trying to break a 1024 bit RSA key used by Motorola to sign the boot and recovery partitions on the Motorola Milestone. If this key could be broken, we would be able to sign our own boot/recovery images, which would enable us to run custom kernels and recovery images on the Milestone.It is, of course, very unlikely that a 1024 bit RSA key can be broken. To break an RSA key, a large (1024 bits in our case) number n has to be factorized (split into its prime factors, of which there must be exactly two in the case of an RSA key). If those two prime numbers (p, q with p*q=n) can be found, the private key can be calculated instantly.
One of the best algorithms to factor large integers is the General Number Field Sieve, but even this algorithm would run several centuries on recent hardware to factor a 1024 bit integer. The GNFS guarantees a correct solution, but only after it has ended, so it is not feasable to use it.
This project uses the very naive bruteforce approach. In the worst case this algorithm will find the solution only after the earth is long gone (as in ‘never’ ;)), but there is a minimal chance that we’re lucky and guess the correct key. To be honest, I cannot think of many events that are more unlikely to happen than finding the key, but it won’t do any harm to try, so i encourage everyone with a few unused cpu cycles to follow the instructions below and join MilestoneRSA!


One commentOn MilestoneRSA: (hoffentlich) irgendwann offenes Milestone
Pingback: Das perfekte Pad … | blogdoch reloaded ()